Policy Packs
All the policies you need...
are in your ISO 27001:2022 ISMS Policy Pack
From implementation, through certification and beyond
Policies...
Your ISMS Toolkit includes:
Management Requirements
Policies that cover the 7 mandatory ISO 27001 Requirements Clauses that you can edit to reflect the Context, Leadership, Planning, Support, Operation, Performance Evaluation and Improvement within your organisation.
Annex A Control Policies
Pre-written control policies that includes all of the 93 ISO 27001 controls, including: Information Security Policy, Policies and Procedures for Information Security, Technical Operating Procedures, Business Continuity Policy, Data Protection Policy, HR Policies and Processes, Physical and Environmental Security Policy and Security Incident Management Policy.
All of the documents can be used 'out of the box' and, where necessary, adapted to suit your business's specific requirements
What you'll get:
Requirements Clauses
The mandatory ISO 27001 Requirements Clauses
Annex A Control Policies
Information Security Policies and Procedures
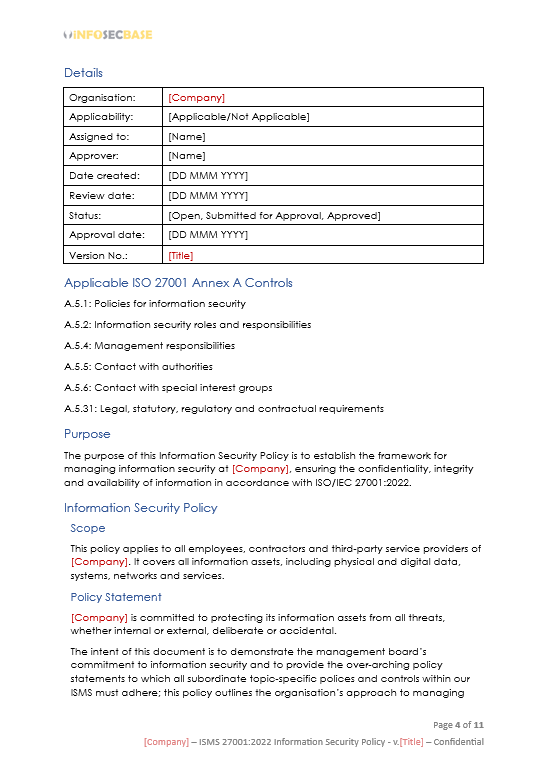
The purpose of this Information Security Policies and Procedures document is to establish the framework for managing information security at your organisation, ensuring the Confidentiality, Integrity and Availability (CIA) of information.
This document mainly focusses on your Information Security Organisational policies and procedures.
Information Security Policies & Procedures
This policy includes all the information security controls that are not covered by topic-specific policies, including Policies for information security, Information security roles and responsibilities, Management responsibilities, Contact with authorities, Contact with special interest groups and Legal, statutory, regulatory and contractual requirements.
Technical Operating Procedures
This policy includes all your ISMS Technical Controls, including: User endpoint devices, Capacity management, Protection against malware, Management of technical vulnerabilities, Configuration management, Information backup, Redundancy of information processing facilities, Clock synchronisation, Use of privileged utility programs, Installation of software on operational systems, Networks security, Use of cryptography, Application security requirements, Secure system architecture and engineering principles, Outsourced development, Separation of development, test and production environments, Test information, Protection of information systems during audit testing.

Human Resources (HR) Policy
The purpose of this policy is to define the responsibilities and processes related to human resources (People) security at your organisation, ensuring that all employees, contractors and third-party service providers understand their responsibilities and are suitable for the roles for which they are considered.
This policy outlines the Human Resources processes for Screening (Pre-Employment Screening for Prospective Employees, Screening for Contractors and Third-Party Service Providers, Screening Documentation and Records), Terms and Conditions of Employment (Employment Agreements, Information Security Responsibilities, Disciplinary Actions, Access Control, Termination and Change of Employment) and Responsibilities after Termination or Change of Employment.
Physical and Environmental Security Policy
The purpose of this Physical and Environmental Security Policy is to establish guidelines and controls to protect your organisation's physical assets and environments from unauthorised access, damage and interference.
This policy aims to ensure the security of physical locations, equipment and infrastructure through Physical and Environmental Security Controls: Physical security perimeter, Physical entry, Securing offices, rooms and facilities, Security monitoring, Environmental controls, Working in secure areas, Clear desk and clear screen, Equipment security and siting, Security of equipment and assets off-premises, Storage media, Supporting utilities, Cabling security, Equipment maintenance, Secure disposal or reuse of equipment).


Data Protection Policy
The purpose of this policy is to establish the framework and procedures for protecting personal data within your organisation, ensuring compliance with data protection laws and regulations and supporting the requirements of ISO/IEC 27001:2022.
This policy outlines the principles and practices to protect data against unauthorised access, disclosure, alteration and destruction through Data Protection Principles (Lawfulness, Fairness and Transparency, Purpose Limitation, Data Minimisation, Data Masking, Accuracy, Storage Limitation, Integrity and Confidentiality, Accountability, Data Subject Rights), Data Protection Measures (Data Inventory and Mapping, Consent Management, Third-Party Management, Data Protection Impact Assessments [DPIAs]) and Data Leakage Prevention to detect and prevent the unauthorised disclosure and extraction of information by individuals or systems.
Business Continuity Policy
The purpose of this Business Continuity Policy is to establish the framework for your organisation to respond to and recover from disruptions to its operations, ensuring the continuity of critical business functions.
The policy covers Business Continuity Responsibilities, Business Impact Analysis (BIA), Risk Assessment, Business Continuity Plans (BCPs), Testing and Exercises, Incident Response and Recovery and Communication.

Security Incident Management Policy
The purpose of this policy is to establish a framework for managing security incidents within your organisation to minimise the impact on your information assets and to ensure a timely response.
This policy aims to ensure that Security Incidents are managed through Incident Management Planning and Preparation Process, Event Assessment and Decision Process, Incident Response Process, Learning from Incidents Process and Evidence Collection Process.
“If you spend more on coffee than on IT security, you will be hacked. What's more, you deserve to be hacked.”
Richard Clarke